Showing posts with label a. Show all posts
Showing posts with label a. Show all posts
Wednesday, February 18, 2015
Java program to check whether a number is prime or not

class prime
{
public static void main(String...s)
{
int n,i;
n=Integer.parseInt(s[0]);
for(i=2;i<n;++i)
{
if(n%i==0)
break;
}
if(i==n)
System.out.println("
Number is prime");
else
System.out.println("
Number is not prime");
}
}
Monday, February 16, 2015
C program to reverse a number

#include<iostream.h>
#include<conio.h>
void main()
{
clrscr(); //to clear the screen
long n,rev=0,d;
cout<<"Enter the number:";
cin>>n;
while(n!=0)
{
d=n%10;
rev=(rev*10)+d;
n=n/10;
}
cout<<"The reversed number is "<<rev;
getch(); //to stop the screen
}
Fill Colour of bar s based on a condition in Pentaho CDE
This post will talk about conditional colours of bars with below like scenarios.
Sample Scenario :
Print bar color as red when bar value <=2000
Print bar color as green when bar value >2000 and <10000
Print bar color as black when bar value>=10000
Scenario 2 :
When representing -Ve values on charts .. this kind of representation is preferable.
Code is Taken from Reference links :
function changeBars(){
var cccOptions = this.chartDefinition;
// For changing extension points, a little more work is required:
var eps = Dashboards.propertiesArrayToObject(cccOptions.extensionPoints);
// add extension points:
eps.bar_fillStyle = function getColor(){
var val = this.scene.vars.value.value;
if(val > 0 && val <= 5000){
return red;
}
else if(val > 5000 && val <= 50000){
return green;
}
else{
return black;
}
};
// Serialize back eps into cccOptions
cccOptions.extensionPoints = Dashboards.objectToPropertiesArray(eps);
}
NOTE : I have tried directly in Extension points but it did not work.
Sample output 1 :

function changeBars(){
var cccOptions = this.chartDefinition;
// For changing extension points, a little more work is required:
var eps = Dashboards.propertiesArrayToObject(cccOptions.extensionPoints);
// add extension points:
eps.bar_fillStyle = function getColor(){
var val = this.scene.vars.value.value;
if(val == 26297.2900){
return black;
}
else{
return blue;
}
};
// Serialize back eps into cccOptions
cccOptions.extensionPoints = Dashboards.objectToPropertiesArray(eps);
}

References :
http://translate.google.com/translate?&ie=UTF-8&sl=&tl=en&u=http://www.redopenbi.com/group/ctools/forum/topics/colores-en-bar-chart?commentId=2400100%3AComment%3A103280&xg_source=activity&groupId=2400100%3AGroup%3A73260
OR
http://www.redopenbi.com/group/ctools/forum/topics/colores-en-bar-chart?commentId=2400100%3AComment%3A103280&xg_source=activity&groupId=2400100%3AGroup%3A73260
OR
http://forums.pentaho.com/showthread.php?150582-Bar-chart-colors-dynamically-changed-based-on-data-value-Along-with-JavaScript-vars
Sample Scenario :
Print bar color as red when bar value <=2000
Print bar color as green when bar value >2000 and <10000
Print bar color as black when bar value>=10000
Scenario 2 :
When representing -Ve values on charts .. this kind of representation is preferable.
Code is Taken from Reference links :
function changeBars(){
var cccOptions = this.chartDefinition;
// For changing extension points, a little more work is required:
var eps = Dashboards.propertiesArrayToObject(cccOptions.extensionPoints);
// add extension points:
eps.bar_fillStyle = function getColor(){
var val = this.scene.vars.value.value;
if(val > 0 && val <= 5000){
return red;
}
else if(val > 5000 && val <= 50000){
return green;
}
else{
return black;
}
};
// Serialize back eps into cccOptions
cccOptions.extensionPoints = Dashboards.objectToPropertiesArray(eps);
}
NOTE : I have tried directly in Extension points but it did not work.
Sample output 1 :

Sample output 2 :
function changeBars(){
var cccOptions = this.chartDefinition;
// For changing extension points, a little more work is required:
var eps = Dashboards.propertiesArrayToObject(cccOptions.extensionPoints);
// add extension points:
eps.bar_fillStyle = function getColor(){
var val = this.scene.vars.value.value;
if(val == 26297.2900){
return black;
}
else{
return blue;
}
};
// Serialize back eps into cccOptions
cccOptions.extensionPoints = Dashboards.objectToPropertiesArray(eps);
}

References :
http://translate.google.com/translate?&ie=UTF-8&sl=&tl=en&u=http://www.redopenbi.com/group/ctools/forum/topics/colores-en-bar-chart?commentId=2400100%3AComment%3A103280&xg_source=activity&groupId=2400100%3AGroup%3A73260
OR
http://www.redopenbi.com/group/ctools/forum/topics/colores-en-bar-chart?commentId=2400100%3AComment%3A103280&xg_source=activity&groupId=2400100%3AGroup%3A73260
OR
http://forums.pentaho.com/showthread.php?150582-Bar-chart-colors-dynamically-changed-based-on-data-value-Along-with-JavaScript-vars
Using a VPN Service – How to Hide Yourself Online

Many Internet surfers want to remain hidden or just left alone. Their reasoning might be founded on something more than just doing something illicit, or illegal. Their reasoning might be based on not wanting to be a part of the ongoing online marketing strategies that scrub personal habits away from everything we do on the Internet. Many companies are eager to get their hands on any Internet surfer’s searching habits, buying and selling preferences, and even their economic status. Most of these companies use this technology to build profiles from the information they garner to know exactly what the online surfer is interested in purchasing before they ever start looking.
Creating Anonymity
The easiest way to hide personal buying habits and other individualized data is to create an anonymous connection online, through a VPN (virtual private network). Using a VPN, the online surfer’s browser will not be recognized by intrusive eyes attempting to pry into personal information and habits. A VPN service creates anonymity by reassigning the computer’s true IP address in an exchange for an anonymous one. This will instantly create a barrier that hides the Internet surfer’s actual data including their region, name and physical address, along with the ISP (Internet service provider) that is being used.
Also Read: Tips on How to Have Better SEO Results with Link Building
A VPN service works as an intermediary between the user and the remote location or website. All requests generated from the user, or the visited website, must go through the virtual private network server. This avoids any man-in-the-middle attackers or cyber-thieves attempting to invade the Internet surfer’s privacy.
Open Access
Using a reputable VPN service provides the Internet surfer open access to any website online. They can gain instant access to social media networks, blogging sites, and streaming websites. These include Netflix, Hulu, Pandora and others that are often restricted due to high activity bandwidth. Additionally, they can visit gambling sites that have heavy restrictions between countries, and allow them to have full access.
Gaining the ability to surf online, without having any online connection session monitored or blocked, is the simplest way to hide online. A reputable VPN service can provide a continuous secured environment that is anonymous to anyone attempting to intercept personal information and data, from any location around the globe. In some countries, government rules and regulations allow law enforcement to request logs and information anytime they suspect an illegal activity from the anonymous surfer.
Veronica Clyde reviews the best VPN providers at VPNServices.net. She loves to share Online Security, VPN technology and Blogging tips. If interested you can check out a Hide my ass.com review.
Sunday, February 15, 2015
USING YOUR BLUETOOTH ENABLED PHONE AS A MODEM UBUNTU 10 4 LTS
 |
| Using your phone as a modem via Bluetooth |
Author: Kibui Kenneth Maina Wed Sep 1, 4:43PM
CLICK ON AN IMAGE TO VIEW THE FULL SIZE IF ITS TOO BURY
1. Go to http://ubuntu-tweak.com/ and install Ubuntu tweak. (It makes it easy for novices and experienced users to configure and manage Ubuntu).
2. After the installation completes go to Applications>System tools> Ubuntu tweak
 |
| Installed Ubuntu tweak |
4. Check Blueman if it is not already checked and click apply. (install to completion)
5. Turn on your phone and computers Bluetooth. (I am Using the Motorolla l6i for this demo).
 |
| Motorola L6i |
6. Go to System>Preferences>Bluetooth Manager
7. Click on the search button on the Bluetooth manager. All available Bluetooth devices will be detected and displayed.
 |
| Installed Bluetooth manager |
8. Click once on your phone on the Bluetooth manager to select it then go to setup on the top bar of the Bluetooth manager.
 |
| A Paring session |
9. Select custom passkey and key in the code of your choice or use mine 0000 then click forward.
 |
| Putting a passkey |
10. Your phone will ask you if you want to pair, select Yes, it will then ask you for a passkey, enter the passkey that you entered into the computer.
11. You will then be asked if you want to connect to dial up networking click forward, select the network that you are on and click on forward.
 |
| Setting up your broadband connection |
12. You will be informed that your device has been added and connected successfully click close.
 |
| Finalizing the set up process |
13.Your Blue tooth manager should appear as follows.
 |
| Your phone connected as a modem |
14. Your panel will appear as follows (no wireless or wired network, one lighting Bluetooth icon one normal Bluetooth icon.
| Your panel before connecting to mobile broadband |
15. Click on your network icon. Go to Mobile broadband and select your network
 |
| Connecting to mobile broadband Internet on your computer |
16. Your connection will appear as shown, with phone network bars appearing where your network connection is supposed to be.
 |
| Your connected mobile broadband ready to go |
 |
| A mobile broadband connection on your computer |
17. Open your browser and browse away.... (Make sure you have enough credit), for Safaricom users you can convert your airtime to bundles to save on credit by dialing;
- *100#
- select option 1
- select option 2
- select option 2
- Select the appropriate bundles
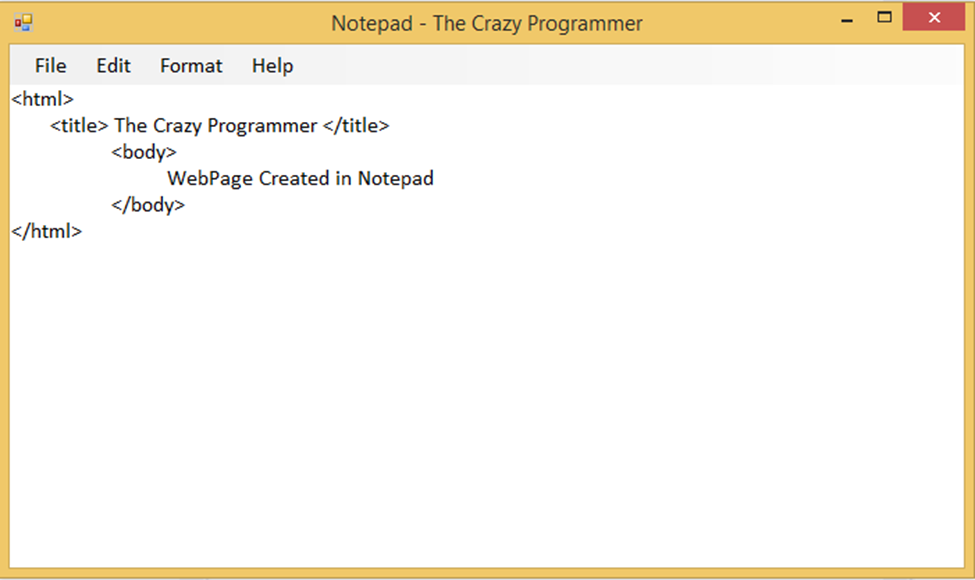
How to Make a Notepad in VB Net
In today’s article I am going to provide you a simple notepad source code developed in visual basic.net. So the notepad uses very simple controls like RichTextBox1 and MenuStrips that is used to design the graphical interface. The code is very simple and self explanatory. This notepad has options like File, Edit, Format and Help.
Also Read: How to Create a Web Browser in Visual Basic
Also Read: How to Create a Web Browser in Visual Basic
How to Use?
- Unzip the rar file we have provided to your favorite folder
- Open Visual Studio, go to File > Open > Project/Solution
- Navigate to the folder where you have extracted the rar file
- Open Notepad.sln file
- Now you can make changes in the program
Download the notepad source code from below link.
- Download Notepad Source Code -
C Program to Count no of alphabates digits and spaces present in a file STORY TXT

#include<fstream.h>
#include<conio.h>
void main()
{
clrscr();
ifstream fin("STORY.TXT");
char ch;
int i,a=0,s=0,d=0;
while(fin)
{
fin.get(ch);
i=ch;
if(i>63&&i<91||i>96&&i<123)
a++;
else
if(ch== )
s++;
else
if(i>47&&i<58)
d++;
}
cout<<"No. OF Alphabates:"<<a;
cout<<"
No. Of Digits:"<<d;
cout<<"
No. Of Spaces:"<<s;
getch();
}
Saturday, February 14, 2015
C program to count number of words in a string

#include<stdio.h>
#include<conio.h>
void main()
{
int i,words=1;
char str[100];
clrscr();
printf("Enter a string:");
gets(str);
for(i=0;str[i]!=
Choosing A Strong Password To Protect yourself from Hackers
 |
| How To Protect Yourself |
Password strength is a measure of the effectiveness of a password in resisting guessing and brute-force attacks. In its usual form, it estimates how many trials an attacker who does not have direct access to the password would need, on average, to guess it correctly. The strength of a password is a function of length, complexity, and unpredictability.
1.Minimum length 8 characters :
►As a rule of thumb, your password must never be below 8 characters. If an attacker happens to use a brute-force attack on your account,which is just trying every possible comobination - with every addition of a character the time taken for the BF attack to crack your password increases exponentially. On average, while it may take just a few minutes to crack open a 6 character password, the time taken for cracking an 8 character password is measured in days and weeks. Assuming your attacker doesnt have a a billion dollar ExaFlop supercomputer after your account, your password is reasonably safe if it is over 8 characters in length(ExaFlop = 10^18 calculations per second).
2.Names and 123 are out of the question :
►The most common passwords are "Name123". Whenever someone is after your account, the first thing they try is common passwords like this. Whoever that person is, you have to assume the worst. It might be some random old guy in his moms garage or maybe your best friend goofing around, you must assume they know everything about you- your name(duh), amily members names, favorite sportsmen, actors, singers- everything. This is the safest way to go. A surprisingly large number of people simply append a 123 to the front or back of a common object thinking they are very smart, but this is the most predictable password there is. Most hackers will start straight away by adding that 123, and if your password is anything like this, youre screwed. Change it ASAP!
One more thing that deserves mention here is the so called "Security Question". Reason being that people who know you will know questions about you like "What was your first pets name?" or "In what town were you born?" - some of the most common security questions. Plus, the people who know you are far more likely to be interested in taking a peek at your private messages than a random old guy in a garage.
Hence, I recommend to never actually use the security questions in the way they are meant to be used. Dont use a direct answer, use something that the question reminds you of. While these may offer another layer of protection from annonymous attackers, they can make cracking your account fairly easy by the people who know you. As an example, someone you know well if left alone with access to your mobile phone might be able to get into your Facbook account with no difficulties at all. Always treat security question as an emergency password, it should be unobvious but easy to remember.
3.Random things? Think again.
►Theres something called a dictionary attack. In a nutshell, it means that your attacker has a dictionary, and a program that will throw every word in the dictionary as an attempt to crack your password. After trying out your own and related names +123, this is what the Hacker is going to try next - A dictionary attack. So it is better if you keep your password well away from any real words.
Although still not a 100% safe, potjack123 is much safer than jackpot123.
4.Turn it around :
►Now a password like aGF$hvYH916!~** is probably as safe as it can get, but its not exactly easy to remember and definitely not easy to type quickly. For this reason, I(for one) turn words around. What I mean by that is instead of using velocity, use yticolev. While as a normal word, its easy to guess but after reversing the characters its unrecognizable.
After a few times, youll get used to it and will be able to type it as quickly as the other one.
5.Throw in symbols and numbers easily :
►If youre like most people, your current passwords probably dont have any weird symbols. But I have a quick way of adding both numbers and symbols to your password.
Heres an example -
567yticolev%^&
Looks weird, right? Well thats the point. What we have here is, the base word velocity - reversed, a 567 at the start (which is much better than a 123), and at the end I have seemingly random symbols which are actually just SHIFT + 567, that is these are actually the ones written above 567 on your keyboard respectively. So all you have to remember is velocity and 567 and within a few days youll be able to type this as fast as any other password but only this one will be relatively impenetrable. (Unless of course you have a supercomputer after your ass, in which case youre screwed XD)
6.Capitalize- The final blow :
►You might be wondering whats the point of adding so much random stuff to your password. Our main goal is basically to expand the number of characters which your attacker has to test to find your password. So - Small alphabets = 26 characters, Numbers = 10 more, Symbols = around 20 more. But if you throw in even just one Capital alphabet, that means your attacker has another 26 freaking characters to test which means, in this case, hes screwed. Reason being the brute-force attack I mentioned earlier. Say your password is the one in the last point with a capital V and Y :
567YticoleV%^&
So thats 14 characters with upper and lower case alphabets, numbers and symbols. Believe it or not, such is the power of exponential growth that it will actually take an average computer BILLIONS even TRILLIONS of years to crack your password. Now even if your insane attacker can somehow get a supercomputer, it would take him several thousands of years to get your password. After even a fraction of this time we can safely assume that he would have lost all his money buying the supercomputer and the will to do whatever he wanted to do with your account. (You can calculate the exact time by using permutations and combinations and the speed of the CPU)
One last thing, by using the same passwords for several different accounts youll only be making the hackers job easier. But yes, remembering a dozen passwords is probably not worth it. For this I suggest making tiny changes. If you use 567velocity for gmail, you can use 456velocity for facebook, 678velocity for yahoo etc. To hack the next account the hacker will have to go through all the combinations all over again and that for him, will probably not be worth it.
So there you have it! For all practical purposes a password like this will be impenetrable throughout your lifetime. (Nevertheless, I still recommend changing your password around twice a year or so. Thats because youre not the only one reading this article.)
C Program to Print an Alphabet from A to L of s in Capital Letter

#include<iostream>
using namespace std;
int main()
{
int i,j,k=1;
char ch;
cout<<"Input an Alphabet in capital letters that you want to print:";
cin>>ch;
cout<<"
";
switch(ch)
{
case A:
cout<<" ";
for(i=1;i<=40;++i)
{
for(j=0;j<=22;++j)
{
if(i==1||i==2||i==21||i==20)
cout<<"*";
else
{
if(j==0||j==20)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
break;
case B:
cout<<" ";
while(k<=2)
{
for(i=1;i<=9;++i)
{
for(j=0;j<=i;++j)
{
if(j==0||j==i)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
}
for(i=1;i<=10;++i)
{
if(i==1||i==10)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
for(i=1;i<=10;++i)
{
if(i==1||i==10)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
for(i=9;i>=1;--i)
{
for(j=0;j<=i;++j)
{
if(j==0||j==i)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
}
++k;
}
break;
caseC:
cout<<" ";
for(i=1;i<=40;++i)
{
for(j=0;j<=22;++j)
{
if(i==1||i==2||i==39||i==40)
cout<<"*";
else
{
if(j==0)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
break;
caseD:
cout<<" ";
for(i=1;i<=18;++i)
{
for(j=0;j<=i;++j)
{
if(j==0||j==i)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
}
while(k<=4)
{
for(i=1;i<=19;++i)
{
if(i==1||i==19)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
++k;
}
for(i=18;i>=1;--i)
{
for(j=0;j<=i;++j)
{
if(j==0||j==i)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
}
break;
caseE:
cout<<" ";
for(i=1;i<=39;++i)
{
for(j=1;j<=20;++j)
{
if(i==1||i==2||i==20||i==21||i==38||i==39)
cout<<"*";
else
{
if(j==1)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
break;
caseF:
cout<<" ";
for(i=1;i<=40;++i)
{
for(j=1;j<=20;++j)
{
if(i==1||i==2||i==18||i==19)
cout<<"*";
else
{
if(j==1)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
break;
caseG:
cout<<" ";
for(i=1;i<=25;++i)
{
for(j=1;j<=20;++j)
{
if(i==1||i==2)
cout<<"*";
else
{
if(j==1)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
for(i=1;i<=10;++i)
{
for(j=1;j<=20;++j)
{
if(i==1||i==2)
{ if(j==1||j==14||j==15||j==16)
cout<<"**";
else
cout<<" ";
}
else
{
if(i==9||i==10)
cout<<"*";
else
{ if(j==1||j==18)
cout<<"**";
else
cout<<" ";
}
}
}
cout<<"
";
}
break;
caseH:
cout<<" ";
for(i=1;i<=40;++i)
{
for(j=1;j<=21;++j)
{
if(i==20||i==21)
cout<<"*";
else
{
if(j==1||j==19)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
break;
caseI:
cout<<" ";
for(i=1;i<=40;++i)
{
for(j=1;j<=30;++j)
{
if(i==1||i==2||i==39||i==40)
cout<<"*";
else
{
if(j==15)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
break;
caseJ:
cout<<" ";
for(i=1;i<=30;++i)
{
for(j=1;j<=28;++j)
{
if(i==1||i==2)
cout<<"*";
else
{
if(j==14)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
for(i=1;i<=10;++i)
{
for(j=1;j<=15;++j)
{
if(i==10||i==9)
cout<<"*";
else
{
if(j==1||j==13)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
break;
caseK:
cout<<" ";
for(i=20;i>=1;--i)
{
for(j=0;j<=i;++j)
{
if(j==0||j==i)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
}
for(i=1;i<=20;++i)
{
for(j=0;j<=i;++j)
{
if(j==0||j==i)
cout<<"**";
else
cout<<" ";
}
cout<<"
";
}
break;
caseL:
cout<<" ";
for(i=1;i<=40;++i)
{
for(j=1;j<=25;++j)
{
if(i==39||i==40)
cout<<"*";
else
{
if(j==1)
cout<<"**";
else
cout<<" ";
}
}
cout<<"
";
}
break;
}
return 0;
}
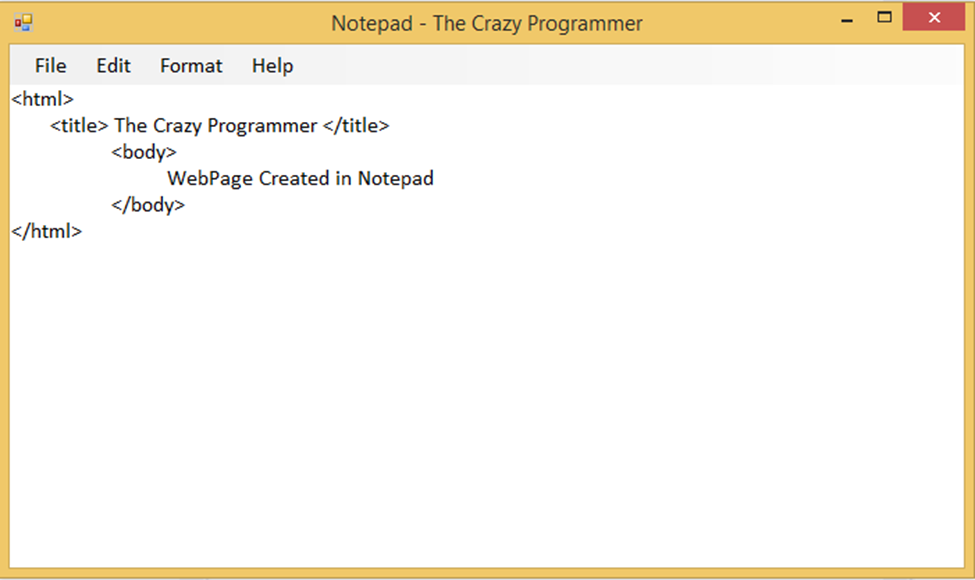
C program to find largest and second largest no from a 2D array
#include<iostream.h>
#include<conio.h>
void main()
{
clrscr();
int a[5][5],big1,big2,n,m,i,j;
cout<<"Enter no of rows and columns(max 5):";
cin>>m>>n;
cout<<"Enter the array:
";
for(i=0;i<m;i++)
for(j=0;j<n;++j)
cin>>a[i][j];
big1=a[0][0];
for(i=0;i<m;++i)
for(j=0;j<n;++j)
{
if(a[i][j]>big1)
big1=a[i][j];
}
big2=a[0][0];
for(i=0;i<m;++i)
for(j=0;j<n;++j)
{
if(a[i][j]>big2&&a[i][j]<big1)
big2=a[i][j];
}
cout<<"
Largest number:"<<big1;
cout<<"
Second largest number:"<<big2;
getch();
}
Friday, February 13, 2015
C program which reads your name from the keyboard and outputs a list of ASCII codes which represent your name

#include<stdio.h>
#include<conio.h>
void main()
{
int i;
char name[50];
clrscr();
printf("Enter your name: ");
gets(name);
printf("
Character ASCII Code");
for(i=0;name[i]!=
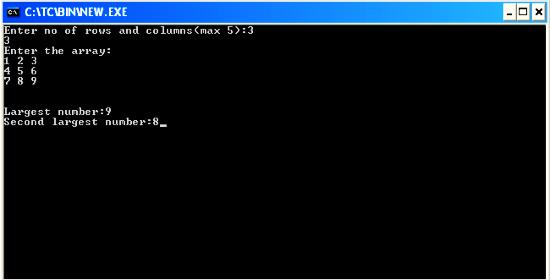
C program to read a matrix of size mxn from the keyboard and display the same on the screen
#include<iostream.h>
#include<conio.h>
void main()
{
clrscr(); //to clear the screen
int a[5][5],n,m,i,j;
cout<<"Enter value of m and n:";
cin>>m>>n;
cout<<"
Enter elemets of the matrix:
";
for(i=0;i<m;++i)
for(j=0;j<n;++j)
cin>>a[i][j];
cout<<"
The Matrix is:
";
for(i=0;i<m;++i)
{
for(j=0;j<n;++j)
cout<<a[i][j]<<" ";
cout<<"
";
}
getch(); //to stop the screen
}
Thursday, February 12, 2015
C Program to Create a Binary Tree Using Recursion Linked Representation
![C Program to Create a Binary Tree Using Recursion [Linked Representation] C Program to Create a Binary Tree Using Recursion [Linked Representation]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjGLSWZDnJJqjV1qzz7_8HUKMvd34NcekdXEWE_BnrB0EMwmONwXoXSjPaKUtk9c-TNQVA2JKbUuuHOR3SYWjH2WuDnW8onVX6Ksqu12JCsexSiUQFlAuINHo2sSs4vos0ueU0mhKloA8el/s640/C+Program+to+Create+a+Binary+Tree+Using+Recursion+%255BLinked+Representation%255D+1.jpg)
What is Binary Tree?
A tree is said to be a binary tree if each node of the tree can have maximum of two children. Children of a node of binary tree are ordered. One child is called “left” child and the other is called “right” child. An example of binary tree is shown in below diagram.
![C Program to Create a Binary Tree Using Recursion [Linked Representation] C Program to Create a Binary Tree Using Recursion [Linked Representation]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEg-DMCVlJV8IlvtlvjHSAwFhxej9vLkzzlEGb1yzy0OJOK2ergbYUjFoowFlRFTr-7vsm5qjFMAGhuxIeOR3e2IHJ1WXWFlB66yTgPgt0xXW16ayJ9OLt-I0raOO8bPiAG14hIF0XQWXdHN/s640/C+Program+to+Create+a+Binary+Tree+Using+Recursion+%5BLinked+Representation%5D+2.jpg)
Creation of Binary Tree Using Recursion
A binary tree can be created recursively. The program will work as follow:
1. Read a data in x.
2. Allocate memory for a new node and store the address in pointer p.
3. Store the data x in the node p.
4. Recursively create the left subtree of p and make it the left child of p.
5. Recursively create the right subtree of p and make it the right child of p.
Also Read: C++ program to create Facebook Login screen
Also Read: C++ Program For Linked List Representation Of Linear Queue
The program is written in C language which allows linked representation of binary tree. Code will be as follow:
#include<stdio.h>
typedef struct node
{
int data;
struct node *left;
struct node *right;
}node;
node *create()
{
node *p;
int x;
printf("Enter data(-1 for no data):");
scanf("%d",&x);
if(x==-1)
return NULL;
p=(node*)malloc(sizeof(node));
p->data=x;
printf("Enter left child of %d:
",x);
",x);
p->left=create();
printf("Enter right child of %d:
",x);
",x);
p->right=create();
return p;
}
void preorder(node *t) //address of root node is passed in t
{
if(t!=NULL)
{
printf("
%d",t->data); //visit the root
%d",t->data); //visit the root
preorder(t->left); //preorder traversal on left subtree
preorder(t->right); //preorder traversal om right subtree
}
}
int main()
{
node *root;
root=create();
printf("
The preorder traversal of tree is:
");
The preorder traversal of tree is:
");
preorder(root);
return 0;
}
In the above program I have used preorder traversal to just show that the tree is created properly or not. You can use any other traversal method here.
6 FAQs on Graphic Designing as a Career

Who doesn’t want to ‘make it big’ in life and rise to the zenith by dint of his enviable career? Of course, there’s no shortcut to success. However, a few smart career moves can lead you to a greener pasture. For example, if you have a creative mind, and believe in teamwork and wish to pursue an ‘offbeat’ career that can offer you a secured future, then you might consider giving graphic designing a try.
Also Read: The Top 10 Websites to create free Logo for your Blog
Also Read: How to Choose the Right Theme for Your Blog?
Here are the FAQs on graphic designing as a vocation:
Q#1: What does a graphic designer do?
By and large, graphic designers are employed to develop designs foe product illustrations, marketing collateral, websites that use computer software and brand identities. They are expected to combine their technical skills with their creativity, and create designs that communicate with the targeted audiences. A graphic designer might work independently, or get placed at different companies.
Q#2: Do you need to pursue any vocational course to become a graphic designer?
To become an expert graphic designer, you need to familiarize yourself with software applications like Adobe Photoshop, Adobe InDesign, Adobe Illustrator, Adobe PageMaker, Corel Draw and the like. A number of agencies offer courses, which are customized to help aspiring graphic designers to proceed in their career. However, it doesn’t take much time to complete the courses, and the course fee is generally kept minimal. After completing the course from a reputed institution, you can earn a living for yourself.
Q#3: Which company to choose?
Since there has been a mushroom growth of institutions offering web designing courses, you might wonder about the ‘right’ institution to join. Ideally, look for an institution which:
- Has been providing web designing course for long.
- Trains you to overcome any professional hazards in the long run.
- Provide in depth knowledge in the skills-in-demand
- Employs experts in the field to train the students.
- Helps in placement after the course is over.

Q#4: Will this profession suit you?
It takes more than technical expertise and a creative bend of mind to become a graphic designer. You need to acquire some soft skills as well. Such as:
- You need to be a stickler for perfection.
- You need to be diligent and ever eager to learn new things.
- You need to be open to suggestions and criticisms.
- You should be able to meet the deadline and deliver the work as and when needed.
Q#5: How to gain experience in this field?
It’s imperative to gain experience to build your confidence and hone your designing skills. This will help establish your reputation as an expert over time. To acquire experience, consider:
- Volunteer your services to any non-profit organization or a local school.
- Helping a family friend/relative by designing their wedding invitation cards.
- Designing your own greeting cards.
- Selling your creations in the local stores.
Also Read: Top 5 Tools to Create Interesting Infographic
Also Read: Top IT Certification Programs for Beginners in 2014
Q#6: How much salary to expect?
As a beginner, you might expect getting around 8500 INR per month. With some experience, you might be able to earn around 20,000 INR. The following factors might affect your salary, though:
- The projects you have undertaken
- Your job location
- The size of the company/design firm you work for.
- Your career responsibilities.
Q#6: Where can you find institutions that offer graphic designing courses?
You might find institutions offering graphic designing courses in almost all the major cities in India. There are a number of institutions are offering graphic design courses in Kolkata. And if you live in the outskirts, then you can also avail graphic designing courses in Rishra, Serampur- they are close to many locations.
Will you like to build your career as a graphic designer? If yes, then start looking for an institution offering graphic designing courses without much ado.
Author Bio:
Henry Carter is associated with a Web development company. He is specialised in Flash web design and database driven e-commerce. Recently he has started writing on Web development and web designing related content and likes to share his experience with his readers. Also he runs his own institute to offer graphic design courses, with an intention to provide more scope of employment.
Wednesday, February 11, 2015
C program to print table of a given number

#include<stdio.h>
#include<conio.h>
void main()
{
int i,n;
clrscr(); //to clear the screen
printf("Enter any number:");
scanf("%d",&n);
printf("Table of %d is:
",n);
for(i=1;i<=10;++i)
printf("
%d*%d=%d",n,i,n*i);
getch(); //to stop the screen
}
C program to raise any number x to a positive power n

#include<stdio.h>
#include<conio.h>
#include<math.h>
void main()
{
int x,n,result;
clrscr(); //to clear the scrren
printf("Enter value of x and n:");
scanf("%d%d",&x,&n);
result=pow(x,n);
printf("
Result=%d",result);
getch(); //to stop the screen
}
C program to read a matrix of size mxn and display it on the screen

#include<stdio.h>
#include<conio.h>
void main()
{
int a[5][5],n,m,i,j;
clrscr();
printf("Enter value of m and n: ");
scanf("%d%d",&m,&n);
printf("
Enter elemets of the matrix:
");
for(i=0;i<m;++i)
for(j=0;j<n;++j)
scanf("%d",&a[i][j]);
printf("
The Matrix is:
");
for(i=0;i<m;++i)
{
for(j=0;j<n;++j)
printf("%d ",a[i][j]);
printf("
");
}
getch();
}
C program to find length of a string

#include<stdio.h>
#include<conio.h>
void main()
{
int i;
char str[50];
clrscr();
printf("Enter a string:");
gets(str);
for(i=0;str[i]!=
Subscribe to:
Posts (Atom)